Setting the Record Straight
Before anything else, I owe two people a correction. Keith, G6NHU — I said you posted on Facebook. That was wrong. You posted on your own blog, which is entirely your right, and I should have gotten that right before publishing. I respect Keith. I read what he writes and I take it seriously, even when I disagree — and I do disagree on the question of open-sourcing the hamclock.com backend. I also notice that he's given Brian's alternative project top billing as the preferred path forward.
Similarly, Udo — I attributed a Facebook post to you that was actually someone else posting on your behalf with a link to your site. That wasn't accurate and I'm correcting it here. Udo's coverage has also pointed toward Brian's project as the community's preferred direction.
To his credit, Udo has configured his devices to allow users to choose between backends — giving his clients the option to point at hamclock.com or Brian's server. That's a fair and reasonable approach, and I respect it.
What's interesting is that Keith, Udo, Michael, and several others I know and respect have all landed in essentially the same place — with remarkably similar framing, at roughly the same time. I can only speculate about what conversations led to that alignment. There must have been one heck of a Teams meeting (speculating) — and I wish someone had sent me the invite.
I don't think any of these people are acting against the community. I think they're acting in their own business interests, which is entirely human and entirely understandable. What I do think is that the full technical picture of what's actually happening may not have made it into those conversations, and that's what this post is here to address.
Michael has passed the torch to Udo, who has stepped in to support his customers. I genuinely hope we can build a productive working relationship. If Udo's clients are going to rely on a backend, they deserve to know that hamclock.com is professionally maintained, has formal continuity built in, and is not going anywhere.
Philip Gladstone, creator of PSK Reporter, will shortly be passed a second set of keys as project trustee and will be prepared to keep this infrastructure running if I'm ever out of the picture. The "what happens if Bruce gets hit by a bus" question has an answer. This is not a one-person operation with no safety net.
I'd like Udo to feel confident pointing his clients to hamclock.com. I think we can get there. That door is open.
Hacking, Scraping, and Passing It Off as Their Own
The community is being asked to rally behind Brian's project as the responsible, community-supported alternative. My server logs tell a different story about how that project is allegedly being kept alive — and Elwood's logs would tell the same story, if anyone could still see them.
Between March 1 and March 4, 2026, two AMPRNET-allocated IP addresses made a combined 12,144 HTTP requests to hamclock.com, consuming approximately 588 MB of bandwidth — pulling map imagery, VOACAP propagation calculations, PSK Reporter feeds, and space weather data. Essentially the full suite of what this server produces.
| IP Address | Requests | Bandwidth | Role | Network |
|---|---|---|---|---|
| 44.27.129.23 | 7,823 | 539 MB | Primary Proxy | AMPRNET / US |
| 44.27.23.154 | 4,311 | 48 MB | Secondary Proxy | AMPRNET / US |
| 44.27.37.66 | 10 | 0.8 MB | NAT Gateway — AF4H | AMPRNET / US |
| 44.32.64.64 | 0 * | — | CSI Scraper (UK) | AMPRNET / High Wycombe |
* 44.32.64.64 showed zero requests to hamclock.com but is actively scraping clearskyinstitute.com and passing that content off as its own service.
These were not HamClock users. They were proxies — allegedly intercepting real client requests and re-serving my content to downstream devices without permission, without attribution, and without ever picking up a phone or sending an email to ask.
Let's be direct about this: the only reason to proxy something that is already free is to pass it off as your own work. There is no other explanation. If your intent was to help the community, you would ask. You would collaborate. You would not silently intercept thousands of requests per day and re-serve the output under your own banner.
The same infrastructure is allegedly running the same play against clearskyinstitute.com simultaneously — and as of this writing that scraping is ongoing. Additional proxies operating from other geographic locations have been identified and will be documented and published as the analysis is completed. Screenshots from this period show content appearing on Brian's service that matches exactly what was live on my server at the same moment — and I have the screenshots to prove it.
The Open Source Argument
Let's also be honest about where the open-source backend argument actually leads. Nobody wants to stand up a server for this. It costs money, it requires sustained technical effort, and the reason people love HamClock is precisely because it just works. Elwood built something genuinely extraordinary — one of the finest pieces of amateur radio software ever written — and fragmenting its backend into a DIY free-for-all will turn that extraordinary product into something unmaintained, unreliable, and eventually abandoned.
I have hundreds of emails from real operators who want exactly one thing: a clock that works, with a backend that stays on. That is what hamclock.com provides. That is not a legacy worth dismantling.
The Trail Leads to a Name
A reverse DNS lookup on 44.27.37.66 — one of the AMPRNET addresses observed directly browsing hamclock.com — returns:
AMPRNET is a block of IP addresses — 44.0.0.0/8 — allocated exclusively to licensed amateur radio operators worldwide by the Amateur Radio Digital Communications organization (ARDC). Think of it as a private internet for ham radio. Addresses are assigned by callsign and governed by ARDC's Terms of Service, which prohibit commercial use and activity that is detrimental to amateur radio. Every 44.x.x.x address traces back to a specific licensed operator.
AMPRNET uses callsign-based DNS naming by convention. AF4H resolves publicly through the FCC Universal Licensing System to Donald J. McMorris, Jr., of Villa Rica, Georgia. You can look him up yourself on QRZ.com and LinkedIn. I have screenshots of both profiles preserved in the event that either one is quietly updated or taken down.
The high-volume scraping IPs share the same 44.27.x.x range and almost certainly route through that same NAT gateway — placing Brian's alleged scraping operation and what follows on the same network backbone.
The Google Cloud Scans
During the same window, three Google Cloud Compute Engine instances conducted what appears to be a deliberate, distributed vulnerability reconnaissance campaign against hamclock.com. A fourth IP performed a liveness check exactly 32 seconds before the scan began — confirming the target was live before launching.
| IP Address | Timestamp (UTC) | Activity | Network |
|---|---|---|---|
| 35.225.82.182 | 03/Mar 18:53:13 | GET / — Liveness check | Google Cloud |
| 34.26.81.167 | 03/Mar 18:53:45 (+32s) | 7× HEAD — Directory scan | Google Cloud |
| 34.48.175.57 | 02/Mar 20:05:35 | 7× HEAD — Directory scan | Google Cloud |
| 34.94.197.27 | 02/Mar 00:36:15 | 7× HEAD — Directory scan | Google Cloud |
Each instance executed exactly seven HEAD requests against an identical directory list. Each used seven different spoofed user-agent strings. Each was deployed from a separate Google Cloud region. Spaced 12–20 hours apart over a 42-hour window. This is not someone accidentally bumping into a server. This is a methodical operation designed to probe for weaknesses while staying under the radar.
Seven requests. Seven different browsers. Seven different devices. All within the same second. From a single IP. That is the signature of automated tooling with user-agent randomization — not a human being browsing a website.
According to his publicly available LinkedIn profile, Donald McMorris is "allegedly" currently employed as a Data Center Technician at Google in Villa Rica, Georgia — a role he has "allegedly" held for approximately 15 years. His personal amateur radio infrastructure is "allegedly" the source of the content scraping operation documented above. The Google Cloud vulnerability scans "allegedly" originated from instances "allegedly" deployed by someone with "allegedly" intimate knowledge of Google's cloud infrastructure. Someone with that background and that tenure would "allegedly" have a precise understanding of exactly what a distributed, user-agent-rotating, ephemeral-instance reconnaissance campaign looks like — and would "allegedly" know far better than to run one against a community radio server. But what do I know.
The Response from ARDC
Two formal forensic incident reports were filed — one with ARDC 44Net Program Manager John Burwell (KI5QKX), and one with Google Cloud Trust & Safety. Here is ARDC's response in full:
I'll leave it to the reader to assess what that response means in context. The reports are documented, the evidence is preserved, and the logs don't lie. John Burwell may have found it easy to look the other way. I doubt Google will be quite as accommodating. Mr. McMorris may want to log into LinkedIn soon — "allegedly" to update his status from Data Center Technician to "Open to Work."
The Proof is in the Data
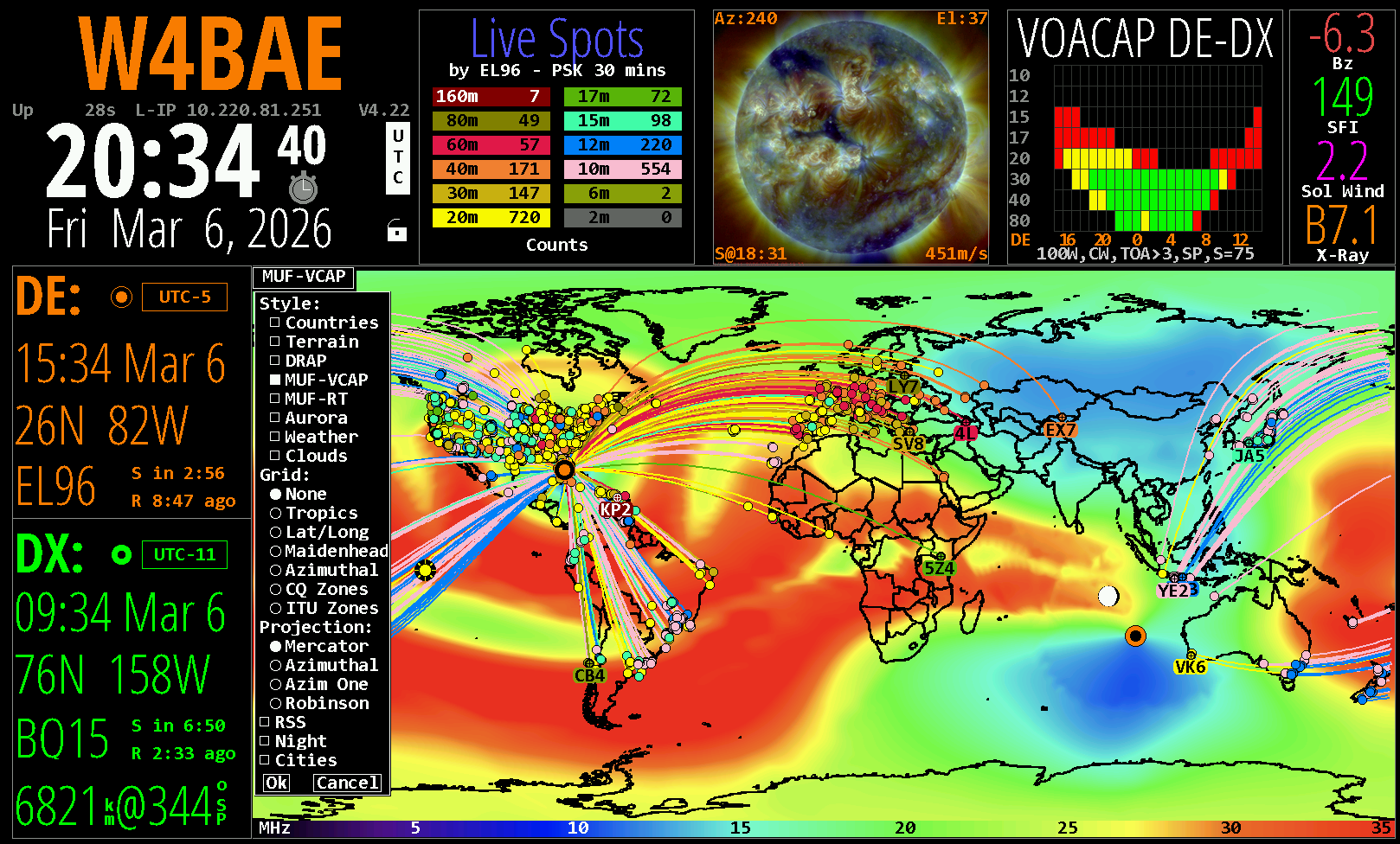
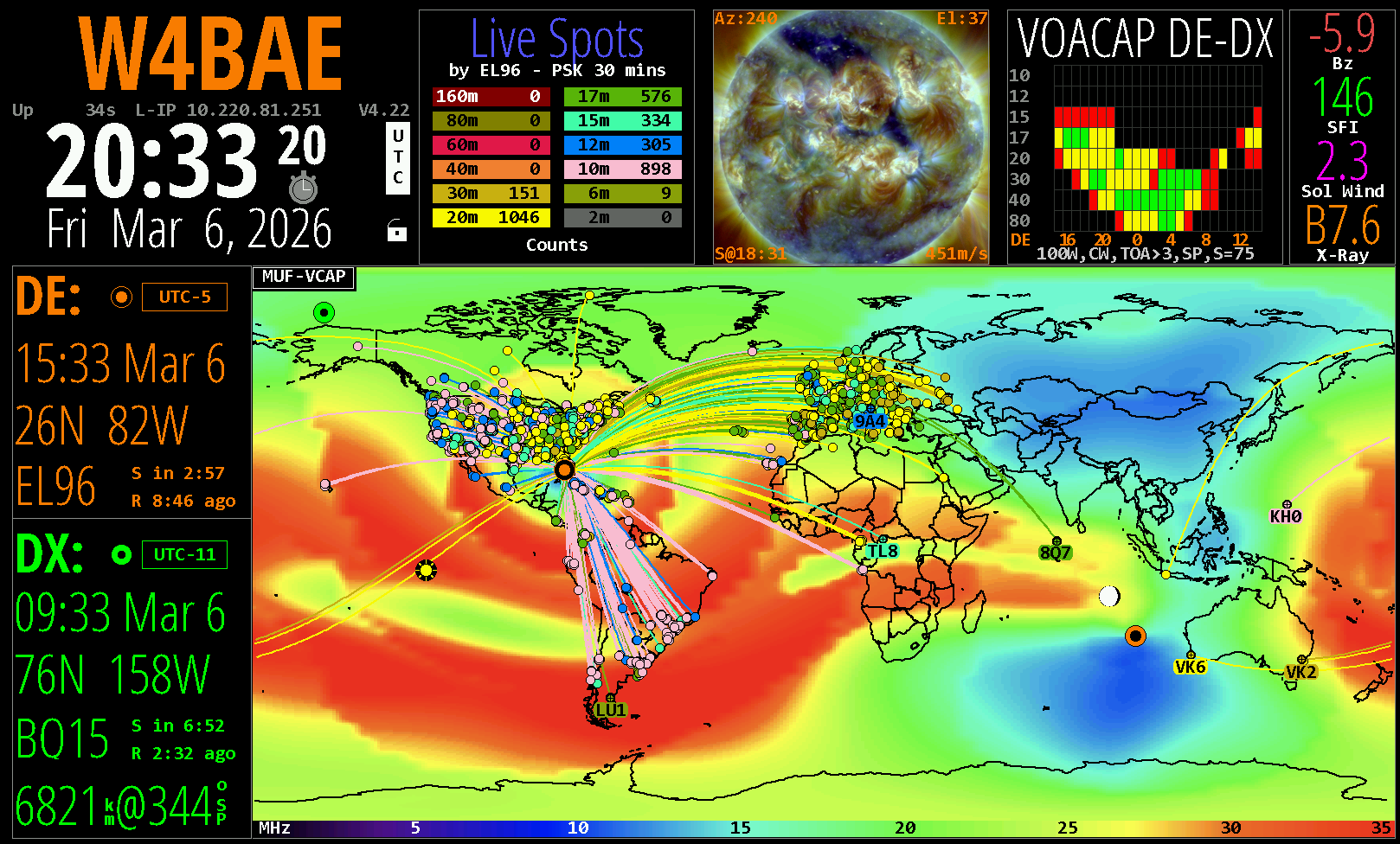
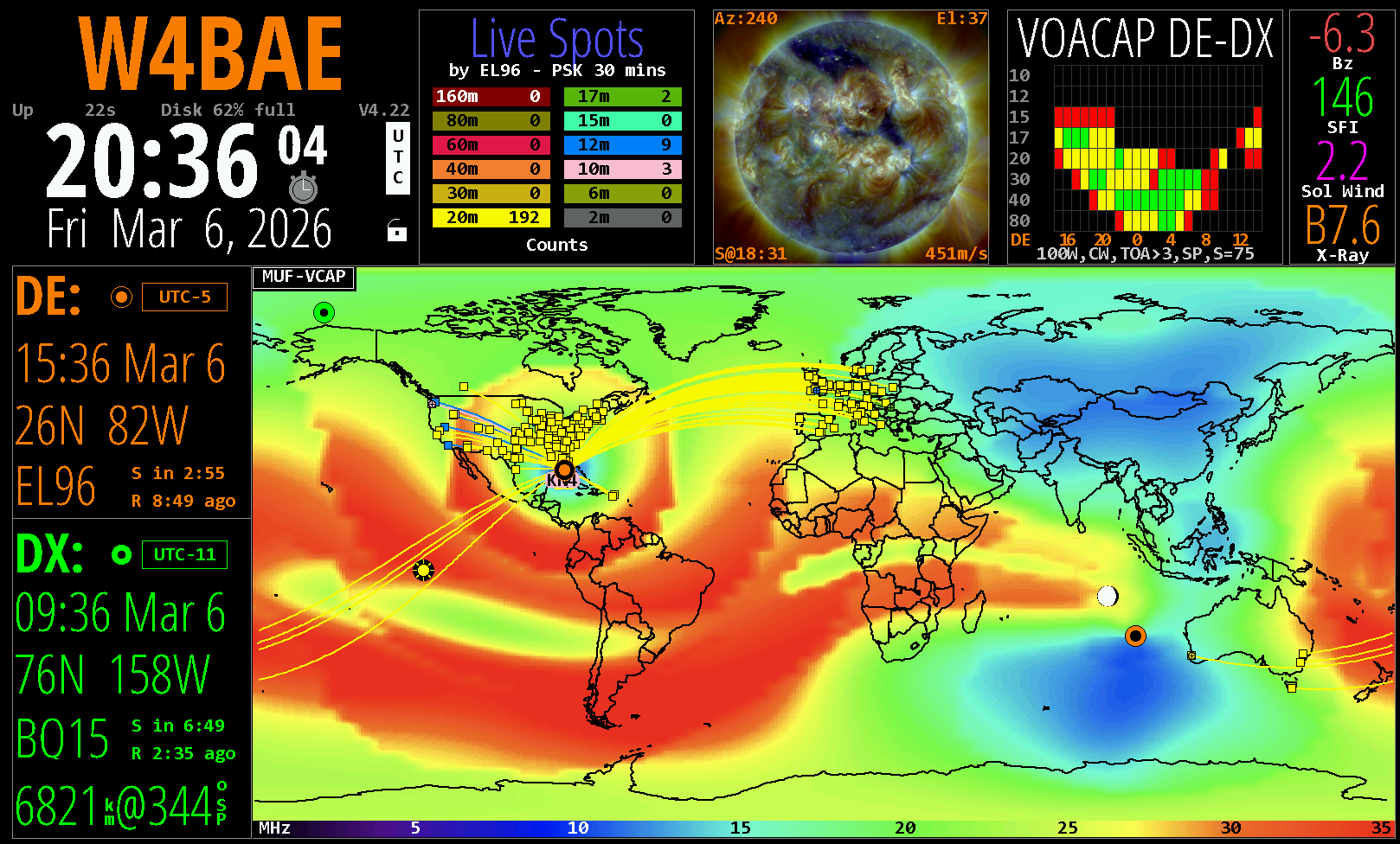
Below are screenshots from hamclock.com, ClearSkyInstitute, and Brian's server. Look closely at the VOACAP band conditions widget across all three. Notice something? The only one that looks different is mine — because I actually generate it. I run the VOACAP propagation engine natively on this server. Brian's is allegedly pulled directly from CSI, and at times allegedly from mine. CSI and OHB look the same because one of them is allegedly stealing from the other.
I am very close to cracking Elwood's exact formula — the secret sauce that makes his VOACAP output match just right. Look at the MUF/VOACAP images — mine are there. Nailed it. The VOACAP DE-DX widget is the one that's almost there, and it's close. Would be further along on that if not for the small matter of running a full-time cybersecurity consulting practice while simultaneously dealing with nonsense from people who seem convinced that everyone around them is less intelligent than they are. You know who you are. Despite all that — look at those images. How about that.
A note on status: VOACAP-TOA is not right and needs to be fixed — that is on the active to-do list. VOACAP-REL needs color correction work — I believe that's also part of Elwood's secret sauce and I'm close to cracking it. These will be addressed. If you see something that needs fixing, send it in — you know how to reach me. Every bug report gets looked at. The list is real, active, and getting shorter.
A Word Before I Get Some Sleep
I want to be honest with you. I am running on a significant sleep deficit going on three weeks now. What has kept me going is the inbox — the emails from real people, the bug reports, the donations to keep this infrastructure running, the notes from operators around the world who took a few minutes to say thank you. I have read every single one of them and I am more grateful than I can adequately express.
I am taking tonight off to get some decent sleep. When I come back tomorrow morning I will keep doing exactly what I have been doing — building the best possible replacement backend for Elwood's extraordinary work, one careful improvement at a time. I have an active to-do list and I am working through it methodically. Please keep those bug reports coming — I will get them all nailed down eventually. Every single one.
73 de W4BAE — Bruce Edrich, CISSP, CPTS
Server Update Notifications
Sign up to receive operational notices from hamclock.com — server events, scheduled maintenance, upgrades, reboots, and outage notifications. This is not a marketing list. It is not spam. It is one operator keeping the community informed about the infrastructure they rely on.